The Differences Between Reverse and Forward Proxy
Forward proxies offer user anonymity and content control, while reverse proxies enhance server performance and security.
Valentin Ghita
Technical Writer, Marketing, Research
Mihalcea Romeo
Co-Founder, CTO
As the volume of web data continues to grow exponentially, the significance of proxy servers in supporting the global web server infrastructure has never been more pronounced. Among these, two distinct types of proxy servers stand out: reverse proxies and forward proxies. Each type comes with its unique set of capabilities, strengths, and limitations. In this article, we delve into both these types of proxies, examining their functionalities and evaluating various scenarios where each type of proxy server proves to be the most advantageous.
What Is A Proxy Server?
A proxy server acts as an intermediary between a user's device and the internet. It receives requests from users, forwards them to web servers, and then returns the server's response to the user. This setup provides several benefits, including improved security, enhanced privacy, and better control over internet usage. Proxies can be used in a variety of environments, from corporate networks to personal computing, for different purposes like content filtering, security enhancement, and load balancing.
What Is A Forward Proxy?
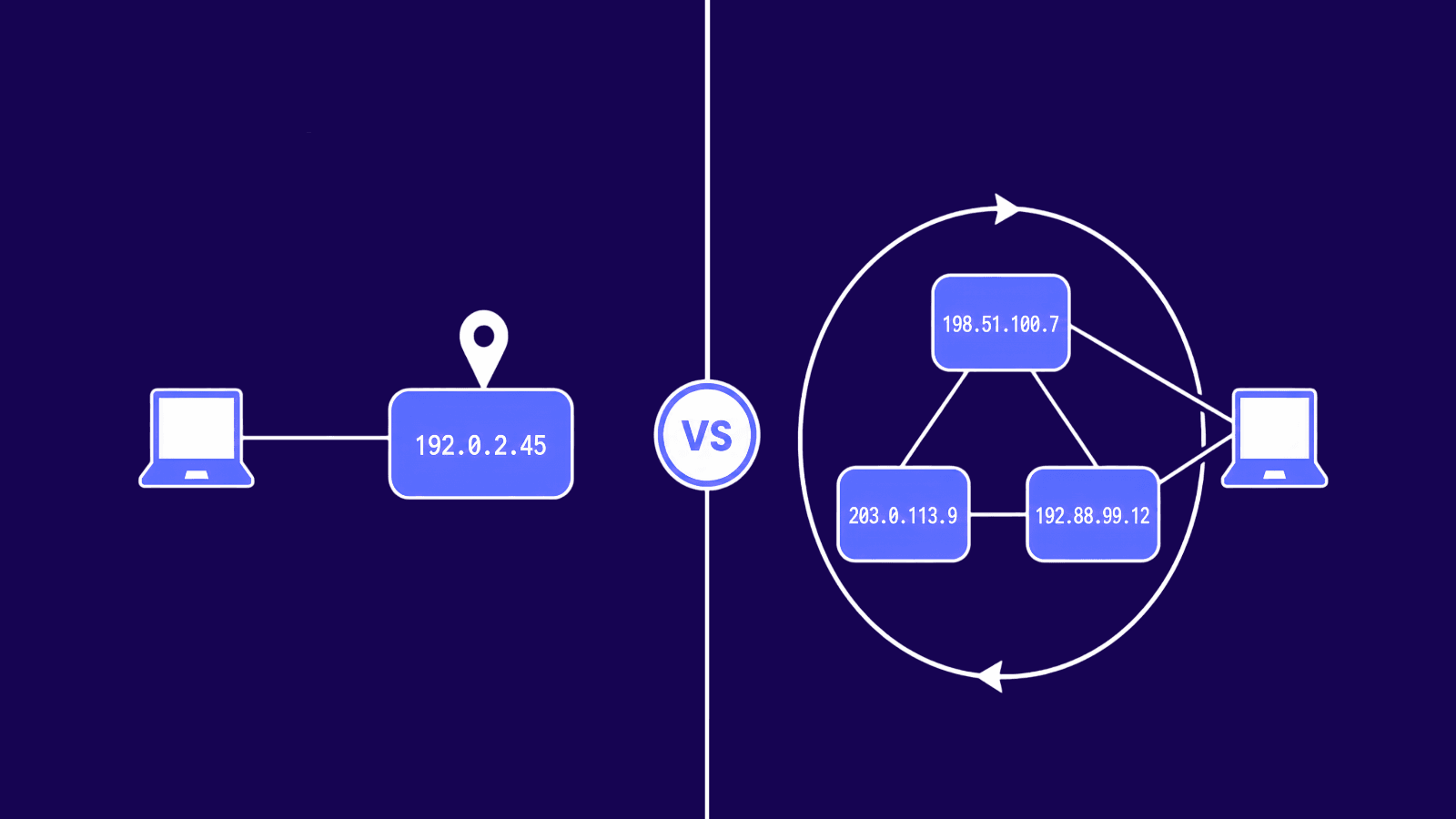
Typically, when discussing proxy servers, the reference is often to the more commonly known type: the forward proxy. Positioned at the forefront of user interaction, a forward proxy acts as an intermediary between users and the web servers they wish to access. In this setup, user requests are first routed through the forward proxy, which then forwards these requests to the intended web page. Responses from the internet are received by the proxy, which subsequently relays them back to the user. To the internet server, it appears as though the request originated from the proxy server, not the user.
This architecture enables the forward proxy not only to cache data for quicker response to future requests but also to serve as a pivotal point for access control and security within a private network. By masking user's original IP addresses, it also plays a crucial role in preserving user anonymity.
Types Of Forward Proxies
Forward proxies come in various forms, each offering unique advantages depending on their source and method of IP address allocation. The two primary categories are:
Residential Proxies: These proxies are assigned genuine IP addresses by an Internet Service Provider (ISP) and are associated with a physical address. They are often perceived as more legitimate by web services due to their association with a residential ISP.
Datacenter Proxies: Unlike residential proxies, datacenter proxies acquire their IP addresses from a secondary corporation, typically a data center. These proxies are not directly linked to an ISP and can offer greater anonymity and efficiency in web traffic management.
Each type serves different use cases, with residential proxies being ideal for tasks that require a high level of legitimacy, such as web scraping, while datacenter proxies are often favored for their speed and cost-effectiveness in situations where a large number of IP addresses are needed quickly and temporarily.
What is Forward Proxy Used For?
Forward proxy, positioned between the user and the broader internet, primarily serve individual users or internal network clients. It is used for:
User Anonymity:
Hiding user IP addresses from external servers, thus maintaining privacy and security.
Internet Access Control:
Restricting and monitoring internet usage within an organization.
Content Filtering:
Blocking access to specific websites or content, often in educational or corporate environments.
Bandwidth Savings and Improved Speed:
Caching frequently accessed content to reduce bandwidth usage and improve load times.
What Is A Reverse Proxy?
A reverse proxy server, in contrast to a forward proxy, is positioned at the network's edge, interfacing with clients on behalf of backend servers. Employed primarily for bolstering security, improving speed, and ensuring reliability, a reverse proxy intercepts client requests, directs them to the appropriate server, and then relays the server's response back to the client as though the proxy itself were the origin. This layer of abstraction ensures that direct contact with the origin server is obscured, enhancing server anonymity.
Reverse proxies are indispensable not for individual consumers but for service providers and high-traffic websites. They serve as digital shields for web servers, enhance website load times, and distribute traffic to prevent server overload. Beyond these functions, reverse proxies are integral for processes like load balancing, content caching, and managing SSL encryption, all critical for maintaining a robust, efficient, and secure web presence.
Types Of Reverse Proxies
While reverse proxies uniformly serve as intermediaries, they can be categorized based on their operational features into two primary types: standard reverse proxies and load balancers.
Standard Reverse Proxies: These are the traditional form of reverse proxies that take a client's request, forward it to the designated server for processing, and then return the server's response to the client. The primary use of standard reverse proxies is to enhance security by concealing the characteristics and location of the backend server.
Load Balancers: Operating as a specialized type of reverse proxy, load balancers distribute incoming requests across multiple server instances. They not only manage the traffic among various servers but also optimize client-server communication. This specialization is particularly effective in balancing the load to improve overall network efficiency and to boost speed and server performance.
What Is Reverse Proxy Used For?
Reverse proxies, located between external users and internal servers, are used predominantly for server-side benefits, such as:
Load Balancing:
Distributing incoming traffic across multiple servers to optimize resource use and prevent any single server from becoming overloaded.
SSL Termination:
Handling SSL encryption and decryption to offload these tasks from internal servers, enhancing performance.
Caching Content:
Storing copies of frequently accessed content to speed up response time.
Security and Anonymity for Servers:
Hiding the characteristics and locations of internal servers from external users.
Forward Proxy Vs Reverse Proxy
Forward proxies and reverse proxies serve distinct objectives tailored to the needs of different stakeholders in the network communication process. A forward proxy is user-centric, designed to safeguard user anonymity, privacy, and security. By mediating communications with file transfer servers and other online entities, it adds a crucial layer of defense. This allows users not only to shield their online activities but also to access restricted websites and gather data with greater ease.
In contrast, a reverse proxy focuses on enhancing the web server's stability and performance. It manages incoming traffic, distributing user requests efficiently to prevent bottlenecks. Moreover, by concealing the server's identity behind an extra layer of security, it helps safeguard against potential threats, ensuring the server remains protected from direct external attacks.
Conclusion
Forward proxies and reverse proxies are fundamental to the smooth operation of internet services, yet they serve very different purposes. A forward proxy acts as an intermediary on the user’s behalf, primarily providing anonymity and security to individual clients, and facilitating broader access to online resources. On the other hand, a reverse proxy serves as a front for one or multiple servers, optimizing and securing backend operations, and ensuring the integrity and performance of web services.

Buy Backconnect Proxies
Rotating IPs on every request. Scale scraping and automation without manual IP management.